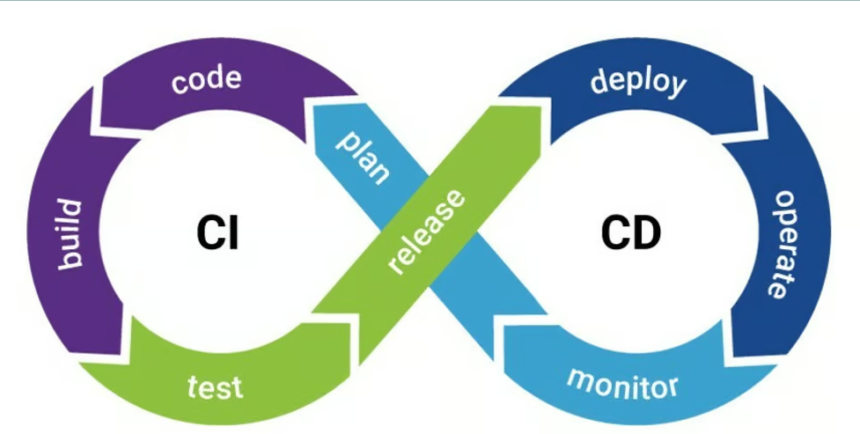
The CI/CD is an abbreviation of Continuous Integration/Continuous Deployment. For pipeline generation, it is necessary to create reliable container images. It is necessary to develop standards for container image security. A compromised pipeline may lead to vulnerable or malicious images.
This can be a source of data breaches inside containerized data. This can cause service disruptions and produce operation inefficiency. A brand may face reputational damage and it can affect market reputation. The release of sensitive data can shatter the confidence level of customers. So necessary to take precautionary steps to ensure the CI/CD pipeline.
Comprehensive Guide to Securing CI/CD
For applying container image security, an organization needs to ensure safe CI/CD pipelines. Below is a comprehensive guide for securing CI/CD pipelines. for container image deployment:
Secure the Pipeline Infrastructure
For securing the CI/CD pipelines create the servers in patches. Necessary to configure the servers securely. The server should be accessible only to authorized personnel. The better container image integrity uses firewalls and network segmentation to restrict access.
Keep an eye on pipeline activities to detect and respond to suspicious behavior. When a business is tracking suspicious activities, it can track branching activities at the different nodes of the network.
For securing the CI/CD pipelines do the following activities.
- Create the servers in patches
- Firewalls and network segmentation
- Tracking suspicious activities
Implement Access Controls
There are different measures to implement container image integrity. A business can secure the CI/CD pipeline by implementing role-based access control(RBAC). This ensures that only authorized personnel are allowed to the CI/CD pipeline. Role-based access control(RBAC) provides an organization to protect sensitive information from the access of others.
For strict access control implementation:
- Role-Based Access Control (RBAC)
- Multi-Factor Authentication (MFA)
- Secrets Management of Sensitive Data
Integrate Security into the Pipeline
Add and integrate security checks early in the pipeline to make CI/CD safe. Necessary to figure out issues before these come into the pipeline. This can be a reason for data breaches. Apply checks at the nodes to protect inside data from security breaches.
You can use the tools like the Rivy, Clair, or Anchore. Scan the container images for vulnerabilities during the production process. Apply repeated checks for compliance with organizational and regulatory standards to avoid data breaches.
- Early Detection of Pipeline Defects
- Automated Vulnerability Scanning
- Policy Enforcement
Strategies to Make CI/CD Safe
Different strategies for making the pipeline of production safe. Try to consider the following strategies, this would make sure your data is protected from breaches.
- Sign and Verify Container Images
- Use Minimal and Trusted Base Images
- Automate Compliance Checks
- Secure the Deployment Process
- Monitor and Protect Runtime Environments
- Educate and Train Teams
- Regularly Review and Update Security Practices
Conclusion
For securing CI/CD pipelines and implementing container image security. Try to apply the strategies given in the article. It does assist in maintaining the integrity, security, and reliability of applications.