Managing traffic through Port 443, the standard port for HTTPS communications, is vital for securing and optimizing web application performance. By adhering to best practices, administrators can ensure secure, efficient data transmission while mitigating potential threats. After reading the following content, you will have a deeper understanding of this point.
Ways to Manage Traffic Through Port 443
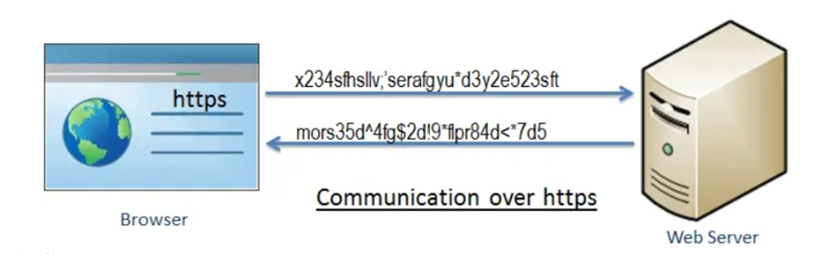
Understanding Port 443
Port 443 is designated for HTTPS traffic, facilitating secure communication over the Internet. It employs SSL/TLS protocols to encrypt data, ensuring privacy and integrity during transmission. Given its role in protecting sensitive information, properly managing traffic through this port is critical for maintaining robust cybersecurity defenses. Effective SSL/TLS implementation is paramount. Ensure certificates are issued by trusted Certificate Authorities (CAs) and use strong encryption algorithms like AES-256. Regularly update SSL/TLS libraries to protect against vulnerabilities such as Heartbleed. Deploy protocols like TLS 1.3, which offers enhanced security features and improved performance over previous versions.

Use Web Application Firewalls (WAFs)
A WAF inspects HTTP/HTTPS requests and blocks malicious traffic before it reaches the server. Configuring a WAF to monitor Port 443 can defend against SQL injection, cross-site scripting (XSS), and other cyber-attacks. Regular updates and tuning of WAF rules ensure adaptive protection against evolving threats. Implementing load balancing distributes incoming HTTPS requests across multiple servers, enhancing availability and reliability. Techniques like round-robin or least connections help distribute traffic efficiently. SSL termination at the load balancer can offload the cryptographic overhead from backend servers, improving overall system performance.
Rate Limiting and Throttling
Rate limiting restricts the number of requests a client can make in a given timeframe, preventing abuse and mitigating DDoS attacks. Coupled with throttling, which regulates the rate at which requests are processed, these measures protect backend resources and maintain service quality. HTTP/2 offers significant improvements over HTTP/1.1, such as multiplexing, header compression, and server push, enhancing the speed and efficiency of HTTPS traffic. Implementing Application-Layer Protocol Negotiation (ALPN) ensures seamless protocol selection between clients and servers, further optimizing performance on Port 443.
Logging and Monitoring
Comprehensive logging and monitoring of HTTPS traffic is essential for identifying and responding to anomalies. Tools like ELK Stack or Splunk can capture detailed logs, which security teams can analyze to detect suspicious activities and improve incident response times. Regular audits help maintain a secure environment. Keeping all software up-to-date, particularly components handling HTTPS traffic, is crucial. Regular patches and updates address emerging vulnerabilities, ensuring that the encryption mechanisms on Port 443 remain robust. Automation tools can streamline the patch management process, reducing the risk of human error.
Educate and Train Staff
Continuous education and training of IT staff on best practices for managing Port 443 are essential. Keeping abreast of the latest cybersecurity trends, threats, and mitigation strategies empowers teams to implement effective security measures confidently. Regular drills and workshops reinforce knowledge and preparedness.
Conclusion
Managing traffic through Port 443 effectively involves implementing robust encryption, leveraging protective tools like WAFs, balancing loads, and employing rate limiting. Enabling modern protocols like HTTP/2, maintaining rigorous logging, and ensuring timely patch management are also critical. By combining these best practices, administrators can secure HTTPS communications, optimize performance, and safeguard sensitive data against threats. Adopting a proactive approach to education and training further fortifies an organization’s cybersecurity posture, ensuring resilience in the face of evolving challenges.